What OSINT is and how to protect yourself
Open-source intelligence (OSINT) is the practice of gathering intelligence from publicly available sources such as social media, news articles, government reports, and online databases. OSINT is used to provide insights that can inform decision-making, strategic planning, and security operations.
To find out more about OSINT, read on.
What is open-source intelligence (OSINT)
OSINT is short for Open-Source INTelligence. It’s what you do when you search the internet to find out if your college sweetheart is still single and where they live. And it can be a lot more, too.
Some people specialize in open-source intelligence gathering and use various tools, techniques, and methods to collect and analyze information from social media networks, websites, public records, news articles, Google Maps, and images. And they do this for different reasons. Journalists use OSINT to do fact-checking. Police use it to search for missing persons. Hackers use it to create personalized phishing attacks, attempt identity theft, or take out a loan in your name.
The origins of open source intelligence
OSINT first gained prominence during World War II. The Office of Strategic Services (OSS), the forerunner to the CIA, was one of the first organizations to use open-source materials in their intelligence gathering efforts. Using publicly available information and media reports, they were able to provide decision-makers with valuable insights into enemy movements and intentions. The OSS used this information to plan missions behind enemy lines and conduct psychological warfare campaigns against German forces.
Since then, OSINT has become an indispensable tool for organizations across all sectors – from government agencies to corporations. Today, numerous companies specialize in providing OSINT services for business purposes.
OSINT techniques
OSINT techniques can be divided into two categories: active and passive. These two approaches differ in how information is collected and the level of engagement required.
Passive OSINT
Passive collection is the most commonly used OSINT technique. It involves collecting publicly available information without direct interaction or engagement with the subject. It relies on existing data and open-source resources readily available on the internet.
Passive collection typically includes activities like analyzing information from resources such as websites, social media platforms, online forums, news articles, and public records. Passive OSINT is valuable for researching and monitoring, making it essential for various fields like journalism, market analysis, and cybersecurity.
Active OSINT
Active OSINT requires you to act on the information you gather from passive OSINT. If you find something interesting, you can contact the person who posted it and see if they have more information or would like to meet with you directly. Active collection often gives more accurate results, but it also relies on direct contact with the subject, increasing detection risk.
OSINT research sources
People engaged in an OSINT investigation collect information from a variety of sources. Depending on their subject of interest, they can use the following OSINT sources:
- Websites: Web pages are a primary source of information for OSINT. This includes news websites, social networking sites, forums, blogs, and other publicly accessible web content. Information on these platforms can range from news articles and public announcements to personal posts and discussions.
- Social media: Platforms such as Facebook, Twitter (“X”), LinkedIn, Instagram, and others are rich sources of OSINT. Users often share personal and sensitive information on their social media accounts.
- Public records: Government agencies and institutions maintain public records, including birth and death certificates, property records, business registrations, court documents, and more. These are readily available on people search sites.
- Online forums and communities: Internet forums, discussion boards, and community websites are places where individuals share experiences, knowledge, and opinions.
- Search engines: Search engines like Google search are indispensable for OSINT as they facilitate keyword- and image-based searches to find publicly available information on the web.
- Research databases: Various databases, such as academic journals, research publications, and government databases, provide in-depth information on various topics. These databases may require subscriptions or access through educational institutions.
- Publicly available NGO and government reports: Many government agencies and non-governmental organizations (NGOs) publish reports, studies, and statistics on various subjects. These documents are typically available for the public to access and can be valuable sources of information.
- Online maps and geospatial data: Mapping services like Google Maps and geospatial data providers offer location-related information that can be used for OSINT, such as identifying physical locations and understanding geographical features.
- Archives and historical data: Historical records, archives, and databases can be valuable for researchers and investigators looking to understand past events, trends, and developments.
- Dark and deep web: The deep web may contain relevant information. However, accessing this information requires specialized tools and expertise.
- Web scraping tools: OSINT professionals may use web-scraping tools and scripts to extract information from websites and data sources automatically.
- Human sources: In some cases, OSINT may involve direct communication with individuals, experts, or sources who possess valuable information or insights.
Most popular OSINT tools
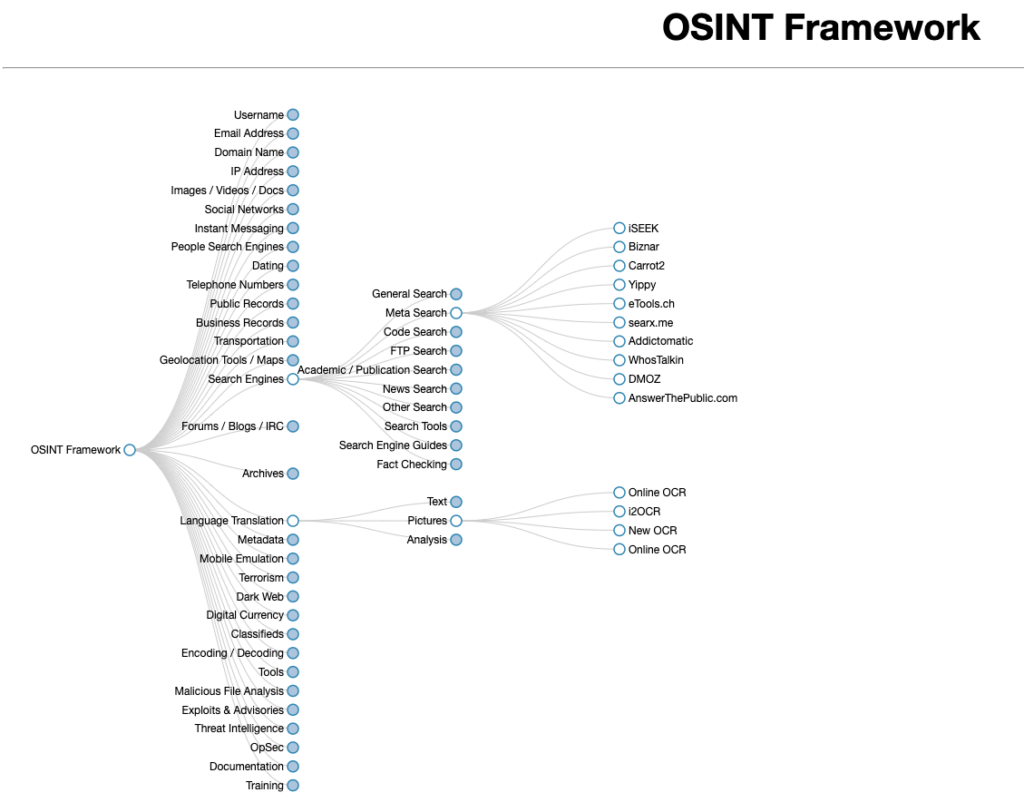
OSINT tools come in all shapes and sizes, and there are many for each purpose. Whatever your need is, there is an OSINT tool for it, and you can find it in the OSINT framework, which is a comprehensive repository of OSINT tools.
OSINT tools are developed by a diverse range of individuals and organizations, including independent developers, cybersecurity experts, researchers, government agencies, law enforcement, and private companies.
The most frequently used OSINT tools can be divided into five categories:
Discovery tools
The most popular of these are search engines, which include both traditional ones such as Google or Bing and specialized OSINT ones like the Shodan search engine.

Other discovery tools include domain reconnaissance tools, which help gather intelligence on domains and their owners, such as WHOIS lookup services or ICANN lookup. As well as username and email search tools (like Hunter) and social media discovery tools that explore social media profiles (like Sherlock).
Scraping tools
Such as web scrapers and social media scrapers, which specialize in gathering information by extracting it from web pages and social media profiles.
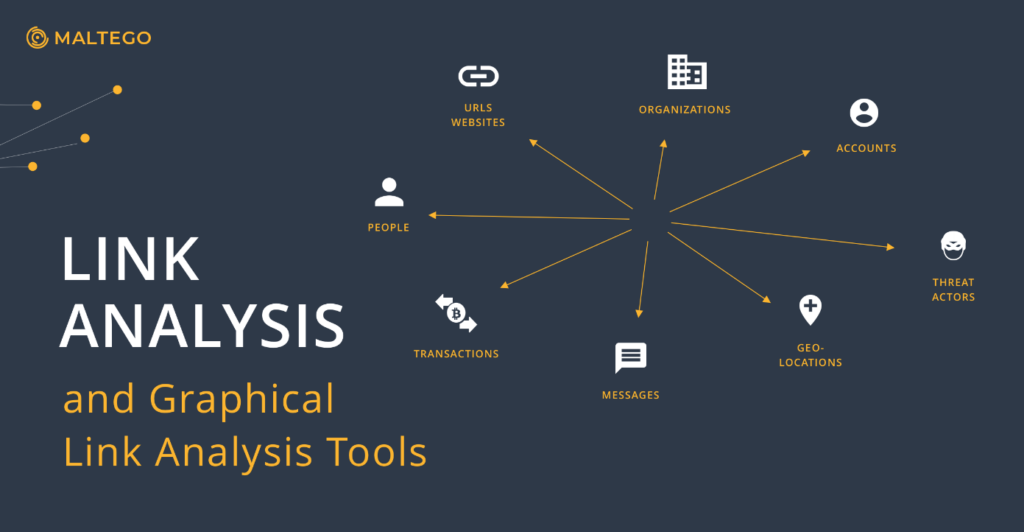
Aggregating and analysis tools
These tools collect and compile publicly available data and then help connect data points and analyze them. Some of these include visualization features to better present the data gathered. Examples of this tool are Gephi and Tableau.
People search sites could also be considered a subset of OSINT data aggregating tools because they gather personal information from different sources.
Dark web monitoring tools
An example of this OSINT tool is DarkOwl, a web crawler that monitors the dark web for specific keywords, organizations, or individuals.
Related: How to find out if my information is on the dark web?
Image and video analysis tools
Tools that extract and analyze data from images and videos, such as Amped FIVE, a forensic video program.
Is OSINT legal?
Yes, it is legal to use OSINT to find information about a person or company. It’s legal because OSINT researchers use public data to gain insights about their subject, which is not a crime in itself.
That said, data collection performed for foreign intelligence agencies could be considered espionage in many countries.
The OSINT regulations
Although OSINT is not illegal, OSINT practitioners in the EU must seek a person’s consent if they aim to conduct a targeted OSINT investigation aimed at them, as stipulated by the GDPR. Unless the practitioner is part of the same household or they are a journalist, that is. Even with signed consent, the data collection must be limited to the bare minimum necessary to answer the investigative question. The intelligence should also be securely stored for no longer than required to close the case.
In the US, in the absence of something like the GDPR, it’s the US intelligence community that publishes guidelines and recommendations. One of these is the OSINT foundation, which develops standards for the OSINT community.
The Department of Homeland Security, in a document dedicated to OSINT, warns that the “information gained from OSINT must be obtained in a way that does not violate existing privacy laws, must not be used maliciously, and must be done only as a necessary means to an end.”
How do organizations and governments use OSINT?
OSINT plays a vital role in national security and counterterrorism, providing authorities with threat intelligence. OSINT is also used by law enforcement to investigate crimes, as well as by financial institutions for fraud detection.
Cyber-security teams use OSINT experts to identify vulnerabilities in networks and systems, eliminate security risks, conduct internal telemetry monitoring, and prevent malware attacks. Investigators can find cyber criminals or trace a missing person through social networks and by analyzing publicly available information. OSINT processes can be leveraged to manage intellectual property violations and prevent fraud.
It is, therefore, not surprising that there is also a growing need for experts in OSINT, and the market share of the open-source investigation industry is projected to grow by 20% between 2023 and 2032.
How do hackers use OSINT?
It is even less surprising that cybercriminals exploit OSINT techniques to perfect their “craft.” OSINT research helps hackers in a variety of ways. The possibilities are limitless. Some of the most obvious ways it can help hackers is by allowing them to:
- Identify their target to prepare a convincing social engineering attack;
- Harvest emails for a phishing or spam campaign;
- Scan a website to identify open ports or vulnerable servers;
- Gain competitive intelligence about a company and its future product releases.
How can you protect yourself from OSINT?
As OSINT relies on your digital footprint to gather intelligence, the best way to protect yourself is by reducing it to a minimum. It’s best to assume that all the data you publish online, whether sensitive information or pictures of your pets, can be discovered in an OSINT investigation.
On top of that, the usual privacy practices apply here:
- Use a private browser and search engine;
- Connect to a VPN to mask your location;
- Implement strong passwords and two-factor authentication whenever possible;
- Use an encrypted email service.
- For the data that’s already out there, use a search engine to conduct a personal OSINT assessment. There is actually a lot you can do to remove your information from the internet and opt out of various data brokers’ operations. Alternatively, you can use a data removal service, like Incogni, and have it remove sensitive information for you. In addition to being a timesaver, a data removal service will send requests to data brokers you’ve never even heard about.
The future of OSINT
The future of open-source intelligence is poised to be transformed by cutting-edge technologies like artificial intelligence, natural language processing, and machine learning. These advancements will enable OSINT analysts to sift through vast amounts of data more efficiently, uncovering hidden insights and patterns. OSINT tools will increasingly harness the power of AI to monitor, filter, and analyze open-source information autonomously, reducing the human workload and enabling faster response times.
Staying vigilant online
Open-sourced intelligence is a powerful tool used across many industries to improve competitive analysis, national security, investigative journalism, cybersecurity, and more. And like all powerful tools, it can be misused, especially without regulation to control it and set boundaries. At a time when information is both abundant and potentially dangerous, it’s essential to safeguard our digital footprint and be mindful of the information we voluntarily share on the internet.
FAQ
Does the FBI use OSINT?
Yes, OSINT is an integral part of the FBI’s intelligence efforts. It helps monitor threats and actors, analyze trends, and support data collection.
What is negative about OSINT?
Depending on where you live, OSINT comes under little or no regulation. This means that people practicing OSINT can invade your privacy without you knowing about it. Data collected thanks to OSINT can result in a targeted cyberattack when in the wrong hands.
What is the opposite of OSINT?
As OSINT stands for open-source data collection, the opposite of OSINT is closed-source intelligence or classified information.