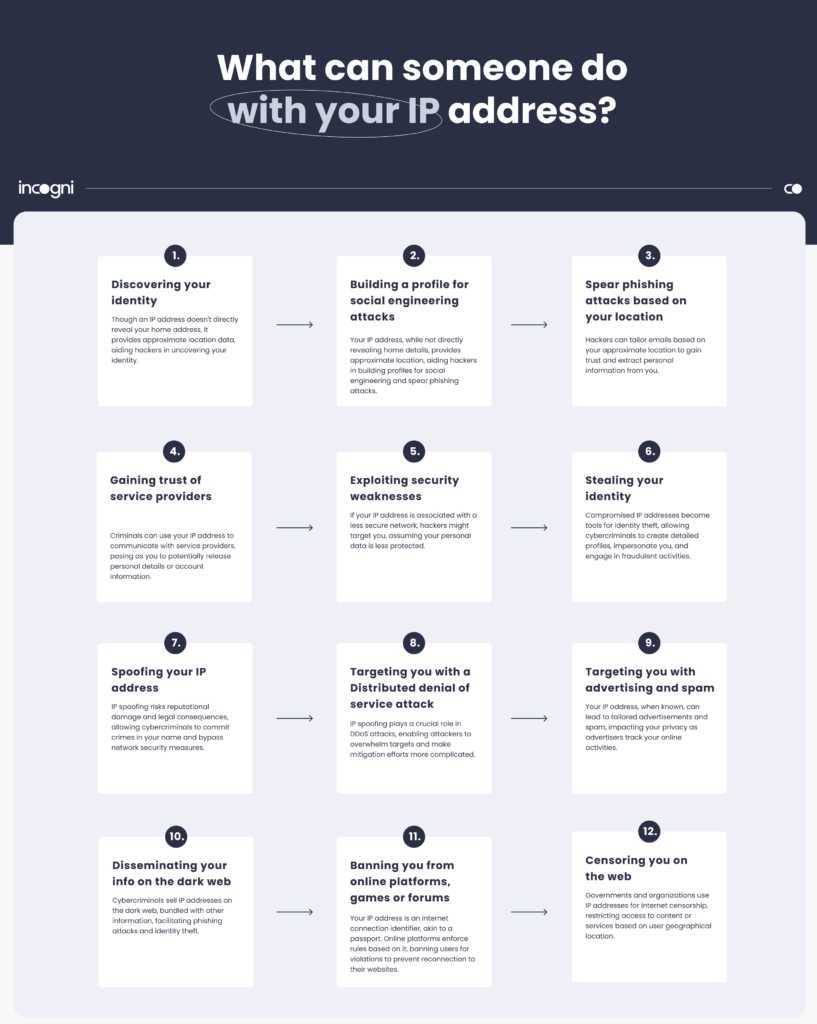
What can someone do with your IP address?
Your IP address is the unique identifier of your device on a given network, it’s what allows online traffic to be routed to where it’s going. Although it’s not considered personal data, it’s still valuable information that many companies and individuals want to get their hands on.
But what can they do with it?
In short, what can someone do with your IP address?
With your IP address, hackers can commit identity theft, launch DDoS attacks, spoof your IP, track your location, access your device, and sell your data on the dark web. This in turn can lead to privacy invasion, personalized spam, service restrictions, and even framing you for illegal activities.
Let’s look at each of these threats in detail.
How can your IP address be misused
If you’re asking yourself what someone can do with your IP, the answer is quite a few things, ranging from minor inconveniences to very consequential cyberattacks.
Discovering your identity
The IP address is not considered personally identifiable information (PII) in itself. It will not reveal your precise home address. However, it does provide approximate location information. This in turn can help hackers discover your identity.
So while IP addresses can reveal your location, having access to your physical name and address can pose different types of risks, from “sending you a letter” to “stealing your identity.”
Related:
With your IP address, a hacker can gather more information about you like your browsing habits or online shopping pattern This information can be used to build a detailed profile that can be used in sophisticated social engineering attacks aimed at manipulating you to reveal your PII.
Spear phishing attacks based on your location
By knowing your approximate location, a hacker can also tailor emails or messages so that they appear to be from local businesses or services you use to gain your trust and make you reveal your personal information.
Gaining trust of service providers
Criminals can use your IP address in communications with service providers, pretending to be you. The IP address makes their request appear more authentic, potentially leading to the release of personal details or account information.
Exploiting security weaknesses
If a hacker discovers your IP address is associated with a less secure network, they might target you for attacks, assuming your personal data is also less protected.
Stealing your identity
When your IP address gets compromised, it becomes a significant tool for identity thieves. By linking your IP address with other pieces of information they’ve gathered, cybercriminals can create a detailed online profile of you. This information can include your browsing habits, the websites you visit, and even your online purchase history. With these data points, they can successfully impersonate you in various fraudulent activities.
Cybercriminals could also use your stolen identity to access or open online accounts, take out loans or make purchases, potentially ruining your credit score and causing long term financial difficulties.
Related: Identity Theft Fact & Statistics
Spoofing your IP address
The risk extends beyond just financial fraud. Identity thieves can use your persona to commit crimes online, spread malicious code, or download illegal content, all under your name.
IP address spoofing is a tactic in which cybercriminals forget the source IP address in their attack, making it appear as though malicious activity is originating from your IP address, not theirs. This can lead to serious reputational damage, and could attract attention from law enforcement, leading to a complicated situation where you might have to prove your innocence.
Moreover, IP spoofing can be used to bypass network security measures. Since many security systems allowlist certain IP addresses, cybercriminals can exploit this by gaining unauthorized access to sensitive areas of the network. They do this by making their traffic appear as if it’s coming from a trusted source.
IP spoofing is often used in distributed denial of service attacks (DDoS).
Targeting you with a Distributed denial of service attack
IP spoofing plays a crucial role in the execution of DDoS attacks, making them more effective and complex. In a DDoS attack, the goal is to overwhelm the target, such as a website or network service, with excessive traffic, causing it to slow down or crush, thus denying service to legitimate users.
By spoofing IP addresses, attackers can conceal their own identity and location, bypass security checks. But they can also generate a massive traffic by spoofing a huge number of stolen IP addresses with the use of bots. This not only increases the volume of the attack but also makes mitigation efforts more complicated, as blocking a single source is ineffective.
Your IP address can be used in a DDoS attack, but you can also fall victim to a DDoS attack if perpetrators know your IP address.
Targeting you with advertising and spam
The dangers of your IP falling into the wrong hands go beyond security concerns, and directly impact your right to privacy. Some internet service providers and advertisers will send you tailored advertisements and unwanted spam based on your IP address and browsing history. They do this by embedding tools such as cookies, tracking URLs and pixels into online content.
These tools collect data on how you interact with various websites and ads. Your IP address, a part of this collected information, reveals your browsing habits and approximate location, allowing for tailor-made ads popping up on your screen, which can be intrusive and overwhelming.
Disseminating your info on the dark web
Being relentlessly targeted with personalized ads is a minor inconvenience compared to this next one. Your IP address, a key element of your online identity, can become a commodity for illegal trade. Cybercriminals are known to sell IP addresses on the dark web, often bundled with other information to facilitate phishing attacks and identity theft. In other words, one sold, your information and profile can lead to more sophisticated fraud attempts and many more attempts, than if it stayed in the hands of just one criminal.
Banning you from online platforms, games or forums
Your IP address serves as a unique identifier for your internet connection, much like a passport or ID document. Online platforms, games and forums will enforce their rules based on the IP address you connect with. If you violate the terms of service or engage in prohibited activities on these platforms, they can ban your IP address to prevent you from connecting to their websites again.
This approach is a great way for platforms to enforce their rules. However, if you share the same IP address with others (for example within the same household), some users may end up being unjustly punished.
You might have experienced this directly if you’re subscribed to a streaming platform like Netflix or Hulu, which often restrict access based on geographical location. If your IP address indicates that you’re in a region where certain moves are not licensed for viewing, those titles won’t be available to you.
Censoring you on the web
An IP address can be a tool for implementing censorship on the internet, as it reveals the geographical location of the user. Just like forums and websites, governments and organizations can also restrict access to certain content or services based on where the user is located. For instance, a country might block social media platforms, news websites or search engines to control the flow of information and prevent dissent.
The use of IP addresses to impose censorship is part of a broader issue of internet freedom and the global digital divide. It shows that control over digital infrastructure in reality means control of information and freedom of expression online.
How others can get ahold of your IP address
You communicate your IP address in many online places every day, so getting hold of your IP address is not that difficult. Moreover, as the IP address is not considered personally identifiable information, your internet service provider doesn’t have to take any measures to conceal it.
Here’s how your IP address can be found.
Connecting to a website
In most cases, when you load a website, the website’s server logs your IP address. Website servers collect this information for various purposes, including analytics, security, and customization. However, it’s important to note that IP address logging and the specific purposes for which it’s used varies among websites. Some websites prioritize user privacy and minimize data collection; others sell it to the highest bidder without batting an eye.
Online ads
Ads and the platforms that deliver them may log IP addresses. Advertisers and ad networks often collect various types of data, including IP addresses, to track the effectiveness of their ads, prevent fraud, and build user profiles for targeted advertising.
Playing online games
Playing online games can expose your IP address to other players. When you connect to an online game server, your device’s IP address is often visible to others in the same game lobby or session. This visibility is necessary for the game server to know where to send the game data, such as your movements and actions, so other players can see and interact with your character.
Phishing attacks
Hackers may launch phishing attacks to harvest your IP address and other sensitive data. Your IP address could be disclosed when you click on a fraudulent link and connect to a website that runs a script to collect information about your device.
Torrenting
When downloading torrent files, the torrent site showcases the IP addresses of the peers list, which consists of other torrent clients concurrently downloading the same file. Hackers among this peer group may be hoping to pilfer users’ IP addresses for potentially malicious purposes.
Internet forums
Many internet forums log users’ IP addresses. Members can be excluded based on their IP address. Admins can better understand usage patterns and user behavior and also detect spamming and trolling by monitoring IP addresses. Check the privacy policies to know if the forums on which you post do this.
Commenting on blogs
The same is true when you comment under blog posts: the administrator may log your IP address. Whether or not they do that should be written in the privacy policy.
Connecting to the same network
Anyone who connects to the same network as you can see your IP address. In the case of a home network, this person will need a strong password (because, hopefully, you set a strong one) to connect to your network.
Through peer-to-peer sharing (P2P)
Users who share a peer-to-peer network with you may see your IP address. Some messaging apps used to rely on P2P in the past, but it’s no longer the case today.
Router vulnerabilities
Your IP can also be discovered by someone gaining unauthorized access to your router.
How to protect your IP address
There are several things you can do to keep your IP address safe. Let’s start with the most commonly used one:
Use a virtual private network (VPN)
A VPN (like Surfshark) is a technology that replaces your actual IP address with the IP of a VPN server. In other words, rather than your real IP address and actual location, to anyone looking at your internet traffic from the outside, you will look as if you were connecting from Germany or the Bahamas.
Use Tor
An alternative to the virtual private network, Tor will keep your IP address private because it redirects your internet traffic through several servers with different IPs (called nodes). However, users often complain that it also slows down their internet connection.
Use a proxy server
Proxy servers can also replace your real IP address, but their configuration requires some knowledge of network environments, which can be off-putting to many users.
Secure your router with a strong password
Rather than the default one it came with when you first purchased it. Make sure to use a long and complicated mix of lower and upper case letters, numbers, and special characters. Use a trusted password manager like NordPass or Bitwarden to make generating and remembering such passwords effortless.
How do I know if my IP address has been hacked?
There are no obvious indicators that someone else is using your IP without your knowledge. That said, your device could be acting in an unusual way. Here are some telltale signs you should be suspicious of:
Unusual network activity: your internet connection is exhibiting unexpected slowdowns and poor performance. Web traffic and data usage are excessive and do not reflect your online activity.
Unauthorized access to accounts: unfamiliar logins to websites and accounts could indicate that your IP address and login credentials have been compromised.
Changes in settings: changes you didn’t initiate could indicate someone has access to your internet-connected devices.
Blocked access: if you suddenly find yourself unable to access certain websites or online services, it might be due to your IP address being blocked as a result of malicious activity
What can you do if your IP address has been compromised
Act immediately if you suspect your IP has fallen into the wrong hands. Run a security scan on all your devices and change your account and router passwords. Then, reach out to your ISP to let them know what happened. They may be able to give you a different IP address.
If you believe the fraudulent use of your IP address involves illegal activities, consider reporting the incident to law enforcement.
How can I see what my IP address is?
Your IP address is assigned to you by your internet service provider. When you sign up with a provider, you receive an IP address for your home network. Each device connected to this network (the network router, phones, laptops, and smart home devices) will have its own unique IP address.
To check your IP address, open a web browser and type “What is my IP address?” You can also use a website like this one. Some search engines will show your IP address directly as the first result on the list.
If you want to avoid using an online tool to check your IP address (some of these sites will log your address along with other information), here is how to find your IP address on various operating systems.
macOS:
- Go to the Apple menu and choose “system settings.”
- Click on “network.”
- Select your active network connection (WiFi or Ethernet).
- Click “details” to see your IP address.
Windows:
- Open the Command Prompt (search “cmd” in the Start menu).
- Type “ipconfig” and press Enter.
- Your IP address will be listed under “IPv4 Address.”
Linux:
- Open a terminal emulator.
- Type “ip addr show” or simply “ip a” and press Enter.
- Find your network interface (e.g., eth0 for Ethernet or wlan0 for WiFi) and the associated IP address.
iOS (iPhone/iPad):
- Go to “settings.”
- Tap on “Wi-Fi.”
- Find your connected WiFi network (it’ll have a checkmark next to it) and tap on the network name.
- Your IP address will be listed under “IP Address.”
Android:
- Open the “settings” app.
- Tap “network & internet” or a similar option depending on your device.
- Select “Wi-Fi.”
- Find your connected Wi-Fi and tap on it.
- Your IP address will be displayed.
What does your IP address reveal about you?
An IP address reveals the general geographic location of your device, but it’s not precise enough to show your exact address. The location data is limited to city or ZIP code. Your IP address is not publicly linked to any sensitive personal information, such as your name or phone number.
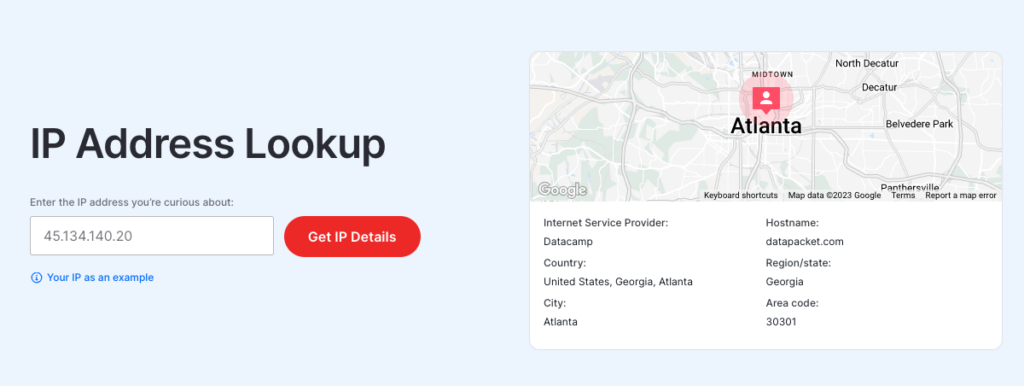
However, while an IP address is not publicly linked to personally identifiable information, it can still provide valuable data to websites, applications, and online services that often track IP addresses for various purposes. These include analytics, security, and targeted advertising. When combined with other data sources, IP tracking can create a digital profile, revealing user preferences, browsing habits, and interests. In the worst-case scenario, it can lead to online identity theft.
FAQ
Can you change your IP address?
Yes, you can change your IP address. The best way to do this is by contacting your ISP and asking them how to do it and the costs involved, if any. You can also try restarting your router.
Does restarting the router change IP?
You can change your IP address by power-cycling your router. Turn it off, wait for at least 10 seconds, then turn it back on. This often initiates DHCP (Dynamic Host Configuration Protocol) renewal. This process may result in your ISP assigning your device a new IP address.
Can an IP address reveal identity?
An IP address cannot reveal a person’s identity, but it can provide some clues about the device’s physical location. This information is limited to a city or a region rather than a precise mailing address.
Can two devices have the same IP address?
No, each device connected to a network must have its own IP address. An IP address serves as a unique identifier for a device on a network, allowing data to be routed to and from that specific device.
Can a cell phone IP address be traced?
Tracing a cell phone’s IP address through mobile data is contingent on legal procedures. Armed with a court order or warrant, law enforcement can request IP-related information from the ISP. Using a VPN or a proxy can make the tracing process very difficult.