Stop Before You Shop – Are Your Shopping Apps Sharing Access to Your Device?
In a recent consumer survey, 88% of respondents reported having at least one shopping app installed on their mobile device1. Given their popularity, you might think these apps are pretty harmless.
In our previous research, we already looked into the Google Play Store data safety section and how to determine the amount of data apps really “share”. This time around, our researchers found something else consumers should be looking out for: ad libraries.
With the biggest shopping season around the corner, our researchers analyzed 640 of the most popular shopping apps from the Google Play Store to uncover how they can potentially affect your online privacy and security.
They found that two-thirds of shopping apps share permissions with an average of 1.8 ad libraries. This means that with each of these apps you grant permissions to, you’re giving the same permissions to not one, but around three companies.
Key findings:
- Two-thirds (65.2%) of analyzed shopping apps use ad libraries.
- The shopping apps that use ad libraries use an average of 1.8, meaning you’d be granting permissions to three companies on average, instead of one.
- 4 out of 5 (83%) analyzed shopping apps request permissions. Some of the most alarming ones are:
- 22.3% request permission to record audio
- 48.3% request permission to access precise (GPS) location
- 15.8% request permission to read your contacts
- 6.1% request permission to read calendar events plus confidential information AND add or modify calendar events and send emails to guests without owners’ knowledge
- 1.6% request permission to read your text messages (SMS or MMS)
- 8.0% request permission to directly call phone numbers
What are ad libraries, anyway?
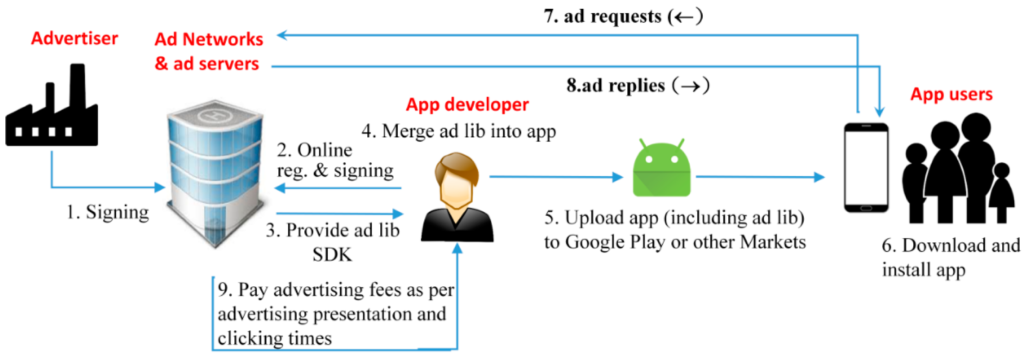
In short, ad libraries are SDKs (Advertisement Software Development Kits) that developers can incorporate into their apps to serve ads. This is a common way for developers to monetize their applications, even if they are free for the user.
These ad libraries are provided by ad networks. The most popular ad network, by far, is Google’s own AdMob, with 61.9% of shopping apps that use ad libraries opting for this network. This is followed by AppsFlyer (36.9%) and Adjust (17.3%).
Why ad libraries mean bad business
Apps running ads might not come as a surprise to anyone. This is nothing new or uncommon, after all. In fact, two-thirds (65.2%) of analyzed shopping apps use ad libraries. But what are the privacy and security implications of this for consumers?
According to a study on ad libraries2, the main issue with apps using ad libraries is that they share permissions with them, giving them access to the same information and functionality as the host app. For example, if you give your shopping app permission to create accounts and set passwords or to read your text messages (both permissions some shopping apps request), you’d be letting any ad libraries these apps use do the same.
The same study found that Android systems don’t distinguish between host app and ad library permission use and won’t prevent the ad library from using all permissions given to the app.
In some cases, external libraries can even add permissions to apps without the developer’s or your knowledge3.
Ad libraries can be malicious, even if the app is not
While an app may be harmless on its own, the ad libraries it includes could contain harmful or invasive code. There have been instances of this happening in the past.
In June 2016, an anti-malware company called Doctor Web revealed that 155 Google Play apps, with an estimated 2.8M+ collective downloads, had a Trojan called Android.Spy.305 embedded in their code. It was uncovered that the Trojan originated from an ad library the apps had used4.
Another instance was reported by Trend Micro in 2017. They discovered that more than 800 Google Play apps had a Trojan called Xavier that could steal user data and download other malicious code onto infected devices. Again, this Trojan originated from an ad library5.
While the potential damage a malicious ad library can cause is clear, avoiding them is trickier. There’s no simple way to determine which networks serve ads on your apps. This makes it difficult to choose which shopping apps are safe to download.
So how can you minimize the risk these ad libraries pose?
The permission types we grant shopping apps
Everyone knows apps require permissions. But to understand what kind of impact these can have on your privacy and security, let’s break down what these permissions are exactly, what they mean, and how many shopping apps request them. While some of these permission types are already clearly alarming at a glance, like your location, messages, and personal information, others might not sound so bad.
Storage permissions, for example, involve storing the app’s files on your device, which makes sense. However, it also allows the shopping app (and its ad libraries) to take pictures and videos. 55.5% of the shopping apps we analyzed requested this specific permission.
While your accounts permissions allow the app to create accounts and set passwords within the app, this permission type can also find accounts on the device (16.7%), add or remove accounts from your device (4.4%), and use accounts on your device (9.4%).
But when you look at the specific permissions each type may include, they start to look more alarming.
Scary-sounding permissions
Starting with some scary-sounding ones, your personal information includes permissions that allow 15.8% of the apps we analyzed and subsequent ad libraries to read your contacts.
6.1% request permission to read calendar events plus confidential information. So not only can they find out what you’re doing and when, but also with whom. Even scarier, still, 6.1% of the shopping apps request permission to add or modify calendar events and send email to guests without owners’ knowledge.
One specific permission under the messages type allows apps to actually read your text messages (both SMS and MMS). 1.6% of the shopping apps we analyzed request this.
Similarly, giving apps permission to use services that cost you money could mean allowing them to directly call phone numbers from your device. As many as 8% of the apps we analyzed request this permission (100% of the apps that request this permission type).
Storage permissions, on the other hand, may sound less alarming. They involve storing the app’s files on your device, which makes sense. However, this permission type may also allow apps to take pictures and videos. 55.5% of the shopping apps we analyzed requested this specific permission.
This type also includes permission to modify or delete the contents of your USB storage. A whopping 58.4% of the shopping apps we looked at request this.
While your accounts permissions allow the app to create accounts and set passwords within the app, this permission type can also find accounts on the device (16.7%), add or remove accounts from your device (4.4%), and use accounts on your device (9.4%).
Combine this with the 22.3% of apps that request permission to record audio (hardware controls) and 48.3% that request precise location (location), and you’ve got a full surveillance kit on your device.
This information may have left you wondering why shopping apps need permissions like record my audio or read my text messages. We don’t have the answer to that, unfortunately. But our research will help you judge for yourself which apps you feel comfortable downloading.
Combine a few of these permissions together and you’ve got a full surveillance kit on your device.
Popular does not mean safe
If you assumed that well-known and popular apps are safer, you’d be mistaken. It turns out, the opposite is true.
For example, while the top-ranking shopping apps in the U.S. use an average of 1.8 ad libraries, the same as the overall average, they request more permission types (7.5 vs 6.9 overall average). They also request an average of 24.9 permissions (22.3% more than the overall average of 20.4).
Even though our researchers found, in a previous study, that paid apps are more private and secure than free apps, free apps are downloaded 400 times more often6. They are also 2x more likely to use ad libraries7. However, this doesn’t mean that paid apps don’t use ad libraries. Some apps offer both paid and free versions. It’s important to remember that regardless of which account type you create, these types of apps may still include the ad libraries8.
Our researchers split the 640 shopping apps we analyzed into four categories, based on popularity. Comparing them by the number of ad libraries used, permission types requested, and permissions requested, here is what we found:
Popular apps use more ad libraries
Two thirds (65.7%) of shopping apps that use ad libraries use only one. One-third (34.3%) use two or more. How does this correlate with popularity, though?
Four out of five of the most popular apps use ad libraries compared to only half (53.2%) of the least popular apps. However, it’s not the most popular apps, but those with between 1M and 10M downloads that use the most ad libraries, with an average of 1.9.
This is followed by the most popular apps with an average of 1.8 ad libraries and the least popular apps, in last place, with 1.6.
There are 5 shopping apps (1%) that take the cake with how many ad libraries they use, going above 10 each. Not surprisingly, most of them (4 out of 5) belong to the most popular category. Anyone using one of these is granting permissions to not one, but 13 or more companies.
| App | Downloads | Ad library count |
|---|---|---|
| AliShop – Online Shopping Apps | 500,000 | 13 |
| Shopping List – Buy Me a Pie! | 1,000,000 | 13 |
| Super Simple Shopping List | 1,000,000 | 13 |
| Clothes Shop – Fashion & Style | 1,000,000 | 12 |
| Grocery Shopping List Listonic | 5,000,000 | 12 |
The most popular apps request the most permission types
While a high percentage of the least popular shopping apps (71.2%) request permissions, almost all (95.9%) of the most popular ones do. When it comes to permission types, the numbers also seem to increase with popularity.
The most popular apps request the most permission types at an average of 8.2 (out of a possible 12). Meanwhile, the least popular apps request around 5.6.
If we break that down further, we can see that about one-third of the least popular shopping apps request less than 5 permission types, while only 1.1% of the most popular apps do the same. Conversely, 92.6% of the most popular shopping apps request between 5 and 10 permission types versus 66.7% of the least popular ones.
Meanwhile, an additional 6.4% of the most popular shopping apps request more than 10 permission types. None of the least popular apps do this.
The most popular apps request the most permissions
The trend seems to continue much in the same way when it comes to the specific permissions shopping apps request. The most popular ones request the most, with an average of 27, nearly double the average of 14.3 for the least popular apps.
7 out of 10 of the most popular apps request approximate location versus only 3 out of 10 of the least popular apps.
The results are similar for precise location as well, with 8 out of 10 of the most popular apps requesting this permission, while only 4 out of 10 of the least popular apps do the same.
Only 1.1% of the most popular shopping apps request less than 10 permissions. The least popular do a little better at a little over one-third.
The roles reverse when it comes to apps requesting more than 20 permissions. The most popular apps come out on top here with nearly 7 out of 10. Meanwhile, only around 2 out of 10 of the least popular apps request more than 20 permissions.
None of them compare to the 7 (around 1%) of shopping apps that request more than 50 permissions, however. Again, all but one of these apps belong to the most popular category.
And while most of them don’t use many ad libraries, both of the Amazon apps on the list use 2. So if you’re responsible for one of the 500M Amazon Shopping app downloads, this means granting 61 permissions to 3 companies just to use 1 app.
| App | Downloads | Permission count | Ad library count |
|---|---|---|---|
| Amazon India Shop, Pay, miniTV | 100,000,000 | 64 | 0 |
| 淘宝 | 10,000,000 | 62 | 0 |
| Amazon Shopping | 500,000,000 | 61 | 2 |
| Amazon Business: Shop and Save | 500,000 | 60 | 2 |
| PatPat – Kids & Baby Clothing | 10,000,000 | 53 | 1 |
| Shopee 10.10 Brands Festival | 100,000,000 | 52 | 1 |
| Daraz Online Shopping App | 50,000,000 | 51 | 1 |
How do we stop ad libraries from gaining access to our devices?
With all this data about how many and which categories of shopping apps pose the biggest risks, all we can do is be mindful of what we download.
Checking the Google Play Store data safety section is a great place to start. But the information available there doesn’t necessarily reflect how potentially harmful an app can be. Some important information such as whether the app uses ad libraries and, if so, which ad networks they belong to isn’t there.
So what can you do?
- Choose an app with fewer ad libraries. Check AppBrain to find apps that offer the same functionality but use fewer ad libraries.
- Be aware of permissions. Check install-time permissions on the Google Play Store before installing the app and be aware of the runtime permissions you grant manually while using the app. You can also check AppBrain to find apps that request fewer permissions.
- Steer clear of popular apps. Popular apps use more ad libraries, request more permission types, and request more permissions than less popular ones. When in doubt, it’s safer to install apps with fewer downloads (as long as they are from a trusted developer).
Methodology
Our research team analyzed 640 of the most popular shopping apps from the Google Play Store. The apps were classed into one of four categories according to their number of downloads:
- <100k downloads (referred to as the least popular apps)
- 100k – up to 1M downloads
- 1M – up to 10M downloads
- 10M+ downloads (referred to as the most popular apps)
We then compared the categories by the average number of ad libraries used, permission types requested (from 12 categories), and specific permissions requested (from a total of 153 unique permissions possible). All of this data was taken from AppBrain.
Here’s a link to the full research material.
References
- Morrissey, Julia. “Survey: 1 in 3 U.S. Consumers Prefer Mobile Shopping Apps to All Other Channels.” NewStore, May 20, 2022. https://www.newstore.com/articles/survey-1-in-3-consumers-prefer-mobile-shopping-apps/.
- Ming-Yang Su et al., “Using Ad-Related Network Behavior to Distinguish Ad Libraries,” MDPI (Multidisciplinary Digital Publishing Institute, October 9, 2018), https://www.mdpi.com/2076-3417/8/10/1852.
- Rotolo, Paolo. “How Libraries Can Silently Add Permissions to Your Android App.” Medium. Glucosio Project, July 14, 2016. https://medium.com/glucosio-project/how-libraries-can-silently-add-permissions-to-your-android-app-620911d7de6c.
- Doctor Web. “New Trojan Found in 155 Apps on Google Play: 2.8 Million Mobile Devices Already Infected.” Dr.Web. Doctor Web, July 28, 2016. https://news.drweb.com/show/?i=10115.
- Xu, Ecular Mobile Threats. “Xavier: An Information-Stealing Ad Library on Android.” Trend Micro, June 13, 2017. https://www.trendmicro.com/en_us/research/17/f/analyzing-xavier-information-stealing-ad-library-android.html.
- Morelli, Federico. “Sharing Is Not Caring: Android Apps That Can’t Get Enough of You.” Incogni Blog, October 11, 2022. https://blog.incogni.com/sharing-is-not-caring/.
- Han, Catherine, et al. “Do You Get What You Pay For? Comparing The Privacy Behaviors of Free vs. Paid Apps.” 1UC Berkeley, International Computer Science Institute, University of Calgary. Accessed November 17, 2022. https://www.ieee-security.org/TC/SPW2019/ConPro/papers/han-conpro19.pdf.
- Han, Catherine, et al. “The Price Is (Not) Right: Comparing Privacy in Free and Paid Apps.” Proceedings on Privacy Enhancing Technologies 2020, no. 3 (2020): 222–42. Accessed November 17, 2022. https://blues.cs.berkeley.edu/wp-content/uploads/2020/03/paper.pdf
Next steps
Shopping apps aren’t the only or even the worst offenders when it comes to your personal information getting into the wrong hands. Companies called data brokers specialize in gathering, compiling, and selling your information to anyone who’s willing to pay. Luckily, the presence of state data privacy laws means that you can opt out of each individual data broker, like Fast People Search, Fast Background Check, Nuwber, Innovis, Instantcheckmate, Clustrmaps, or WhitePages. Cybercriminals get their hands on your personal data and devise scams to get money or more valuable information from you, or both. Removing yourself from the internet is the nuclear option, but you need not go off-grid to make a real impact.